This is the fifth in a series of posts on Grégoire Chamayou‘s Théorie du drone. My next post on the book will consider Chamayou’s second section, ‘Ethos and psyche‘, in its entirety, and when I’ve worked my way through the book in separate, detailed posts (three more sections to go after the next one) I’ll provide a critical overview of the project as a whole: I hope that will help (I must be doing something right – or wrong – since these posts have been picked up by the splendid ARmy Rumour SErvice, which – despite its equally splendid acronym – is not quite a digital child of the Wipers Times).
8: Vulnerabilities
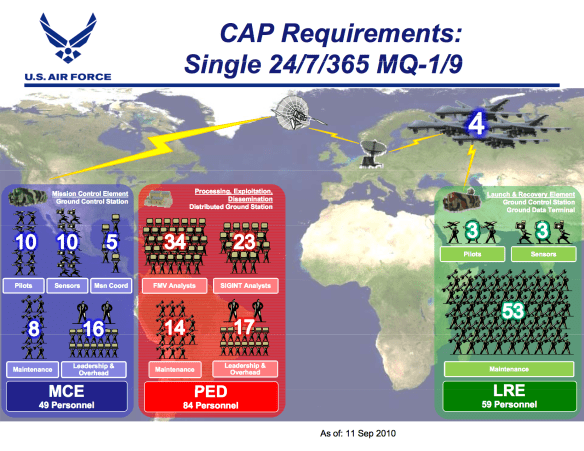
Far from being ‘unmanned’, each US Air Force combat air patrol (CAP) capable or providing coverage 24 hours a day 7 days a week involves a suite of four Predators (MQ1) or Reapers (MQ9) supported by a total of 192 personnel (the exact figures vary and are subject to change, but I’ve taken these from a June 2011 presentation by Colonel J.R. Gear, Director of the US Air Force’s Remotely Piloted Aircraft Task Force).
As you can see from his presentation slide below, most of these (133) are based outside the combat zone, and 84 of those are devoted to ‘PED’ –processing, exploiting and disseminating the feeds from the airborne sensors, especially the full-motion video (FMV) streams.
That leaves 59 who are forward deployed inside the combat zone: three pilots and three sensor operators to handle take-off and landing (which require a line-of-sight link to the aircraft because the Ku-band satellite link used for in-flight operations imposes a response delay that is too great for near-ground manoeuvres). One of the four aircraft is held on the ground for maintenance and, given the technical problems that continue to dog what Jordan Crandall calls the wayward drone, no fewer than 53 people are involved in keeping them flying. [More on drone crashes and glitches here, here and here].
Still, less than half the total complement (44 per cent) is in the combat zone, and all of them work from the relative safety of an airbase.
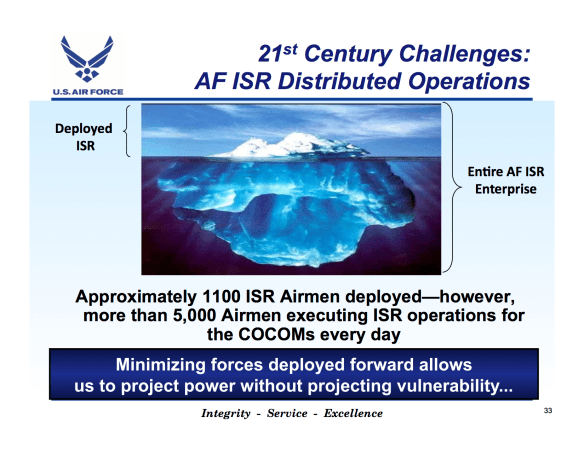
Hence the tag line repeatedly used by the US Air Force to advertise the core advantage of using drones: ‘projecting power without projecting vulnerability’:
I’ve always liked to take metaphors stubbornly literally, and given what is happening to the polar ice we need to ask about the invulnerability of these remote operations.
Chamayou reminds us that in classical mythology and in fable invulnerability has always been a myth; so it is with the drone. He distinguishes two sets of vulnerabilities, one technical and the other political-strategic.
(A) Technical
Chamayou says virtually nothing about the technical imperfections of the Predator and the Reaper, especially the crashes and other failures that I noticed above, but concentrates on two other issues.
(1) ‘Mastery of the air’: At present, Predators and Reapers can only operate in uncontested airspace; they are slow, noisy and far from agile, which makes them highly vulnerable to attack from ground-to-air missiles or conventional strike aircraft. This is not a problem in Afghanistan – even during the invasion US Secretary of Defense Donald Rumsfeld was able to proclaim ‘air superiority’ by 10 October, just three days after launching the first attacks: ‘Afghan skies secure‘ – and according to some reports it never became a serious issue in Iraq either. During Operation Southern Watch, tasked with enforcing no-fly zones over Iraq between the first Gulf War and the US-led invasion in 2003, Eric Reidel reported that
‘Predators were used as bait to stir up Iraqi fighters and air defenses. Surface-to-air missiles eventually brought down two of the drones and an Iraqi fighter jet shot down a third, but it didn’t come that easy to the enemy.’
But that was a contest against a military machine degraded by a sanctions regime. What is now called A2/AD (anti-access, area denial) may well become a serious obstacle to future conflicts. In 2011 Colonel Dean Bushey, deputy director of the joint Unmanned Aircraft Systems Center of Excellence, told Reidel:
“We’re thinking about the next war, thinking about the next fight, thinking about the next campaign… We’ve fought in a very permissive environment where there are no enemy attacks against our unmanned aircraft … It would be foolish for us to imagine that we could continue to fly unmanned systems in an environment that is not only friendly but is not GPS-denied, that is not communications-denied.”
With Obama’s ‘pivot to the Pacific’, the Pentagon has redoubled its efforts to harden its drones for combat (several commentators are sufficiently sceptical about the prospects that they see a renewed commitment to conventional strike-stealth aircraft rather than to UAVs). But perhaps the sharper point is contained in Bushey’s final sentence, and Chamayou spends much more time on this second, vital vulnerability.
(2) ‘Mastery of the waves’: Chamayou documents a series of incidents in which signals were jammed or hacked.
In 2009 the Wall Street Journal reported that insurgents in Iraq had been using commercial off-the-shelf software (costing just $26) to intercept the video feeds from Predators for at least a year, and there was similar evidence from Afghanistan. The Pentagon had known of the vulnerability since the aircraft were deployed over Bosnia in the 1990s, but had not bothered to encrypt the signals because they ‘assumed local adversaries wouldn’t know how to exploit it.’ You might think the solution – encryption of the Common Data Link feeding images to ROVERS (receivers) used by troops on the ground – would be easy, but four years after the story broke Noah Schachtman and David Axe reported that more than half the US fleet of Predators and Reapers were still broadcasting their video feeds in the clear:
”Standard unencrypted video is basically a broadcast to whoever can figure out the right carrier frequency, so essentially, we are simulcasting to battlefield commanders and the opposing force. If that opposing force knows we can see them and from where, they can take better evasive maneuvers.”
 If signals transmitted from the drone can be hacked then, as Bushey noted, so can signals to the drone. This is known as GPS spoofing, and the basic principle is remarkably simple; for a technical exposition that isn’t, see this research paper ‘On the requirements for successful GPS spoofing attacks’ by four Swiss computer scientists (who also propose counter-measures), but for a more user-friendly discussion see Pierluigi Paganini‘s excellent overview of ‘Hacking drones’ here. As Chamayou says, the principle was put into practice in June 2012 , when a group of researchers from the Radionavigation Laboratory at the University of Texas at Austin successfully hijacked a small civilian helicopter-drone at the White Sands Missile Range in Nevada. It was an experiment carried out for the Department of Homeland Security, the target was a tiny Adaptive Flight Hornet Mini (shown above) not a Predator or a Reaper, and the intercept took place at an altitude of less than 20 metres (60 feet) from a distance of 1 kilometre. This year they intend to repeat the experiment but from a distance of 10 kilometres. This is all part of an ongoing project to devise systems to disrupt spoofing, but Chamayou suggests that ‘the air pirates of the future’ will surely try to take control of larger drones from an even greater distance.
If signals transmitted from the drone can be hacked then, as Bushey noted, so can signals to the drone. This is known as GPS spoofing, and the basic principle is remarkably simple; for a technical exposition that isn’t, see this research paper ‘On the requirements for successful GPS spoofing attacks’ by four Swiss computer scientists (who also propose counter-measures), but for a more user-friendly discussion see Pierluigi Paganini‘s excellent overview of ‘Hacking drones’ here. As Chamayou says, the principle was put into practice in June 2012 , when a group of researchers from the Radionavigation Laboratory at the University of Texas at Austin successfully hijacked a small civilian helicopter-drone at the White Sands Missile Range in Nevada. It was an experiment carried out for the Department of Homeland Security, the target was a tiny Adaptive Flight Hornet Mini (shown above) not a Predator or a Reaper, and the intercept took place at an altitude of less than 20 metres (60 feet) from a distance of 1 kilometre. This year they intend to repeat the experiment but from a distance of 10 kilometres. This is all part of an ongoing project to devise systems to disrupt spoofing, but Chamayou suggests that ‘the air pirates of the future’ will surely try to take control of larger drones from an even greater distance.
(B) Political-strategic
Here Chamayou is not addressing wider political, legal and ethical objections to which remote operations are indeed vulnerable – as I’ll describe in later posts – but rather the possibility of more direct responses to the deployment of drones.
 (1) Reprisals: Remote operations radicalise what Martin Shaw described in 2005 as The new Western way of war: ‘risk-transfer war‘. Although Shaw emphasised global surveillance, the minimisation of military casualties and an overwhelming reliance on airpower amongst other things – and his ‘rules of risk-transfer war’ are still essential if depressing reading – it is a sign of how far the world has turned since then that he provided no discussion of remote operations or the incorporation of drones as essential vectors of later modern war.
(1) Reprisals: Remote operations radicalise what Martin Shaw described in 2005 as The new Western way of war: ‘risk-transfer war‘. Although Shaw emphasised global surveillance, the minimisation of military casualties and an overwhelming reliance on airpower amongst other things – and his ‘rules of risk-transfer war’ are still essential if depressing reading – it is a sign of how far the world has turned since then that he provided no discussion of remote operations or the incorporation of drones as essential vectors of later modern war.
Perhaps for this reason Chamayou makes no mention of Shaw, but fastens on a short thesis submitted in 2009 by Major Trent Gibson of the US Marine Corps for the Master of Military Studies from Quantico, ‘Hell-bent on Force Protection’. This was a critique of what Gibson called ‘force protection fetishism’. He traced it back to the US military’s experience in Vietnam but argued that it was alive and well in Afghanistan and Iraq. In a key passage quoted by Chamayou, Gibson wrote:
‘Attempts to armorize our force against all potential enemy threats … shifts the ‘burden of risk’ from a casualty-averse military force onto the populace. In doing so, we have lifted that burden from our own shoulders and placed it squarely upon those who do not possess the material resources to bear it – the civilian populace.’
Gibson was reaffirming one of the central tenets of the new counterinsurgency doctrine issued three years earlier, and he doesn’t discuss drones and remote operations either. But what both FM 3-24 and by extension Gibson objected to was the physical separation of troops from the very people they were supposed to protect. One of its cardinal – strategic – weaknesses – was sequestering troops inside vast, heavily defended Forward Operating Bases from which they issued out on sporadic armoured patrols. It was, in part, on overcoming this siege mentality that the so-called “Surge” in Baghdad was predicated (see “The biopolitics of Baghdad”: DOWNLOADS tab). General David Petraeus‘s ‘Commander’s Guidance‘ could not have been plainer:
‘Live among the people. You can’t commute to this fight. Position Joint Security Stations, Combat Outposts, and Patrol Bases in the neighborhoods we intend to secure. Living among the people is essential to securing them and defeating the insurgents.’
 Remote operations hypostatise that ‘commute to the fight’ (see here). Here is one UAV pilot talking to Der Spiegel:
Remote operations hypostatise that ‘commute to the fight’ (see here). Here is one UAV pilot talking to Der Spiegel:
‘In the morning you carpool or you take a bus and drive into work, you operate for an eight-hour shift, and then you drive back home… Before you were at war 24/7, and when you’re home you’re home. This is different. I do e-mails in the morning, rush to the airplane, come out, go to the [Base Exchange], get myself a hamburger, do some more e-mail, do it again, drive home.’
I’ll say more about that compartmentalisation in my next post – it’s a central concern in the next section of Théorie du drone – but Chamayou’s central point here is that the safety of ‘home’ is illusory and that the war cannot be contained within external ‘danger zones’. He’s not talking about insurgent attacks against US air bases or crew (though one recent story, ‘A day job waiting for a kill-shot a world away’, reported that ‘the Air Force, citing what it says are credible threats, forbids pilots to disclose their last names’). What Chamayou has in mind is the possibility of reprisals within the continental United States more generally: risk transferred back to the American public at large. He explicitly endorses the conclusion to Mike Davis‘s Buda’s Wagon: a brief history of the car bomb, where Davis writes:
‘… every laser-guided missile falling on an apartment house in southern Beirut or a mud-walled compound in Kandahar is a future suicide truck bomb headed for the center of Tel Aviv or perhaps downtown Los Angeles.’
This is not a wild scenario. Here is Michael Boyle on the costs and consequences of drone warfare:
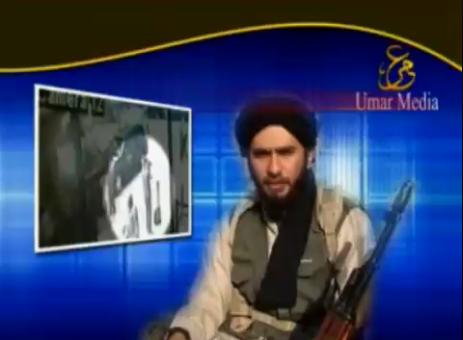
On 21 June 2010, Pakistani American Faisal Shahzad told a judge in a Manhattan federal court that he placed a bomb at a busy intersection in Times Square as payback for the US occupations of Afghanistan and Iraq and for its worldwide use of drone strikes. When the judge asked how Shahzad could be comfortable killing innocent people, including women and children, he responded: ‘Well, the drone hits in Afghanistan and Iraq, they don’t see children, they don’t see anybody. They kill women, children, they kill everybody. It’s a war and in war, they kill people. They’re killing all Muslims.’ In a videotape [below] released after his arrest, Shahzad revealed that among his motives for the attack on New York City was revenge for the death of Baitullah Mehsud, a Pakistani Taliban leader killed in a drone strike in August 2009. While his comments were reported in the American press, the Obama administration never acknowledged that it was revulsion over drone strikes—which Shahzad was rumoured to have seen at first hand when training with militant groups in Pakistan—that prompted his attack.
Although the incident would have strengthened his argument, Chamayou doesn’t mention it. You can find more here; another video featured Pakistani Taliban leader Qari Hussain Mehsud claiming responsibility for what he described as retaliation against US drone attacks in the FATA (more detail here).
 (2) Re-purposing: Drones can be adapted for civilian use – they have been used to monitor herds of caribou and to track the progress of wild fires – and there is a rapidly expanding market for small DIY drones amongst geeks and hobbyists. As Chamayou notes, after reading about the US Army’s small RQ-11 surveillance drone even Francis Fukyama built his own small surveillance drone in his backyard in February 2012. What he doesn’t report, though, is the string of questions that Fukuyama raised in one of his early accounts of the project (Fukuyama now has three drones; updates including video here and here):
(2) Re-purposing: Drones can be adapted for civilian use – they have been used to monitor herds of caribou and to track the progress of wild fires – and there is a rapidly expanding market for small DIY drones amongst geeks and hobbyists. As Chamayou notes, after reading about the US Army’s small RQ-11 surveillance drone even Francis Fukyama built his own small surveillance drone in his backyard in February 2012. What he doesn’t report, though, is the string of questions that Fukuyama raised in one of his early accounts of the project (Fukuyama now has three drones; updates including video here and here):
‘What will the world look like when not just the US but many other countries around the world operate fleets of drones; and when powerful, sophisticated drones are owned by lots of private individuals? What would our attitude be if our enemies could pick off visiting dignitaries as they stepped off the aeroplane in a supposedly friendly country, or attack soldiers in their bases in Europe or Asia? Or if Americans became vulnerable in Florida or New York? Drones might become an inexpensive delivery vehicle for terrorists or rogue states that can’t afford to deliver payloads in ballistic missiles. Some of the remotely controlled aeroplanes that hobbyists build are a third to half the size of their full-scale counterparts. As the technology becomes cheaper and more commercially available, moreover, drones may become harder to trace; without knowing their provenance, deterrence breaks down. A world in which people can be routinely and anonymously targeted by unseen enemies is not pleasant to contemplate.’
The last sentence is pretty rich: the world Fukuyama envisages is already a reality for thousands of people in Pakistan, Yemen, Somalia and elsewhere, and they have to do rather more than ‘contemplate’ it.
Still, these are Chamayou’s questions too. It is precisely the proliferation, diffusion and and above all the down-sizing and down-marketing of small drones that interest him. If they can be ‘demilitarised’ for civilian uses, including Fukuyama’s photographic obsessions, then he contends that it’s perfectly possible for them to be ‘re-militarised’ at remarkably low cost to constitute what Eugene Miasnikov was already calling six years ago ‘an army of suicide bombers on steroids’. This may well be true – and, in a different vein, since October 2012 there have been (conflicting) reports of Israel shooting down two Iranian-made Hezbollah drones, so their adoption by non-state actors seems to be in train already – but it’s still a far cry from the hi-tech world of Predators and Reapers and the globalised killing machine for which they act as spears.
I’ll return to that world in my next summary and commentary on the book.
This completes my extended discussion of the eight chapters that form Part I of Théorie du drone: Techniques and tactics.