New books on the radar:
 Gary Fields, Enclosure: Palestinian landscapes in a historical mirror (California, September 2017):
Gary Fields, Enclosure: Palestinian landscapes in a historical mirror (California, September 2017):
Enclosure marshals bold new arguments about the nature of the conflict in Israel/Palestine. Gary Fields examines the dispossession of Palestinians from their land—and Israel’s rationale for seizing control of Palestinian land—in the contexts of a broad historical analysis of power and space and of an enduring discourse about land improvement. Focusing on the English enclosures (which eradicated access to common land across the English countryside), Amerindian dispossession in colonial America, and Palestinian land loss, Fields shows how exclusionary landscapes have emerged across time and geography. Evidence that the same moral, legal, and cartographic arguments were used by enclosers of land in very different historical environments challenges Israel’s current claim that it is uniquely beleaguered. This comparative framework also helps readers in the United States and the United Kingdom understand the Israeli/Palestinian conflict in the context of their own histories.
There is an excellent review essay by the inimitable Raja Shehadeh over at the New York Review of Books for 18 January; you can read the opening chapter (‘The contours of enclosure’) here; and there’s a brief, illustrated blog post by Gary on ‘the will to resist’ here.
 Caren Kaplan, Aerial aftermaths: wartime from above (Duke, January 2018):
Caren Kaplan, Aerial aftermaths: wartime from above (Duke, January 2018):
From the first vistas provided by flight in balloons in the eighteenth century to the most recent sensing operations performed by military drones, the history of aerial imagery has marked the transformation of how people perceived their world, better understood their past, and imagined their future. In Aerial Aftermaths Caren Kaplan traces this cultural history, showing how aerial views operate as a form of world-making tied to the times and places of war. Kaplan’s investigation of the aerial arts of war—painting, photography, and digital imaging—range from England’s surveys of Scotland following the defeat of the 1746 Jacobite rebellion and early twentieth-century photographic mapping of Iraq to images taken in the immediate aftermath of 9/11. Throughout, Kaplan foregrounds aerial imagery’s importance to modern visual culture and its ability to enforce colonial power, demonstrating both the destructive force and the potential for political connection that come with viewing from above.
Contents:
Introduction. Aerial Aftermaths
1. Surveying Wartime Aftermaths: The First Military Survey of Scotland
2. Balloon Geography: The Emotion of Motion in Aerostatic Wartime
3. La Nature à Coup d’Oeil: “Seeing All” in Early Panoramas
4. Mapping “Mesopotamia”: Aerial Photography in Early Twentieth-Century Iraq
5. The Politics of the Sensible: Aerial Photography’s Wartme Aftermaths
Afterword. Sensing Distance
 Anna Feigenbaum, Tear Gas: from the battlefields of World War I to the streets of today (Verso, November 2017):
Anna Feigenbaum, Tear Gas: from the battlefields of World War I to the streets of today (Verso, November 2017):
One hundred years ago, French troops fired tear gas grenades into German trenches. Designed to force people out from behind barricades and trenches, tear gas causes burning of the eyes and skin, tearing, and gagging. Chemical weapons are now banned from war zones. But today, tear gas has become the most commonly used form of “less-lethal” police force. In 2011, the year that protests exploded from the Arab Spring to Occupy Wall Street, tear gas sales tripled. Most tear gas is produced in the United States, and many images of protestors in Tahrir Square showed tear gas canisters with “Made in USA” printed on them, while Britain continues to sell tear gas to countries on its own human rights blacklist.
An engrossing century-spanning narrative, Tear Gas is the first history of this weapon, and takes us from military labs and chemical weapons expos to union assemblies and protest camps, drawing on declassified reports and witness testimonies to show how policing with poison came to be.
I’ve trailed this before, but now it’s out; there’s an engaging and detailed review by Peter Mitchell at Review 31 here.
 Victor Davis Hanson, The Second World Wars: how the first global conflict was fought and won (Basic Books, October 2017):
Victor Davis Hanson, The Second World Wars: how the first global conflict was fought and won (Basic Books, October 2017):
World War II was the most lethal conflict in human history. Never before had a war been fought on so many diverse landscapes and in so many different ways, from rocket attacks in London to jungle fighting in Burma to armor strikes in Libya.
The Second World Wars examines how combat unfolded in the air, at sea, and on land to show how distinct conflicts among disparate combatants coalesced into one interconnected global war. Drawing on 3,000 years of military history, Victor Davis Hanson argues that despite its novel industrial barbarity, neither the war’s origins nor its geography were unusual. Nor was its ultimate outcome surprising. The Axis powers were well prepared to win limited border conflicts, but once they blundered into global war, they had no hope of victory.
An authoritative new history of astonishing breadth, The Second World Wars offers a stunning reinterpretation of history’s deadliest conflict.
I was alerted to this by Joshua Rothman‘s thoughtful review in the New Yorker just before Christmas.
 Tim Lenoir and Luke Caldwell, The Military-Entertainment Complex (Harvard, February 2018)
Tim Lenoir and Luke Caldwell, The Military-Entertainment Complex (Harvard, February 2018)
With the rise of drones and computer-controlled weapons, the line between war and video games continues to blur. In this book, the authors trace how the realities of war are deeply inflected by their representation in popular entertainment. War games and other media, in turn, feature an increasing number of weapons, tactics, and threat scenarios from the War on Terror.
While past analyses have emphasized top-down circulation of pro-military ideologies through government public relations efforts and a cooperative media industry, The Military-Entertainment Complex argues for a nonlinear relationship, defined largely by market and institutional pressures. Tim Lenoir and Luke Caldwell explore the history of the early days of the video game industry, when personnel and expertise flowed from military contractors to game companies; to a middle period when the military drew on the booming game industry to train troops; to a present in which media corporations and the military influence one another cyclically to predict the future of warfare.
In addition to obvious military-entertainment titles like America’s Army, Lenoir and Caldwell investigate the rise of best-selling franchise games such as Call of Duty, Battlefield, Medal of Honor, and Ghost Recon. The narratives and aesthetics of these video games permeate other media, including films and television programs. This commodification and marketing of the future of combat has shaped the public’s imagination of war in the post-9/11 era and naturalized the U.S. Pentagon’s vision of a new way of war.
Contents:
Induction: The Military–Entertainment Complex and the Contemporary War Imaginary
1. From Battlezone to America’s Army: The Defense Department and the Game Industry
2. Creating Repeat Consumers: Epic Realism and the Birth of the Wargame FranchiseWindows
2.1. The Ludic Affordances of Special Forces
2.2. Franchise Game Business Models
2.3. The RMA in Contemporary Wargaming
3. Coming to a Screen Near You: The RMA and Affective Entertainment
4. Press X to Hack: Cyberwar and VideogamesWindows
4.1. The Narrative Affordances of Hackers and Cyberwarfare
Discharge: Counter-Wargaming in Spec Ops: The Line
This is part of what James Der Derian famously called the Military-Industry-Media-Entertainment complex (MIME), and what I’ve called the Military-Academic-Industrial-Media complex (MAIM). Here is Colin Milburn on the book:
“Locked and loaded, this astonishing account of the ‘military-entertainment complex’ exposes the links between military technologies and popular media, the alignments and affinities among defense agencies, video game companies, and Hollywood studios. With tactical precision, Tim Lenoir and Luke Caldwell show how the militarization of contemporary society is driven less by political interests than by economic interests, revealing the ways in which the entertainment industry and its commercial practices shape the imagination of postmodern warfare. This is a provocative, high-octane book about the war games of everyday life and the future of digital culture. Epic pwn.”
 Maja Zehfuss, War and the politics of ethics (Oxford, March 2018):
Maja Zehfuss, War and the politics of ethics (Oxford, March 2018):
Contemporary Western war is represented as enacting the West’s ability and responsibility to help make the world a better place for others, in particular to protect them from oppression and serious human rights abuses. That is, war has become permissible again, indeed even required, as ethical war. At the same time, however, Western war kills and destroys. This creates a paradox: Western war risks killing those it proposes to protect.
This book examines how we have responded to this dilemma and challenges the vision of ethical war itself, exploring how the commitment to ethics shapes the practice of war and indeed how practices come, in turn, to shape what is considered ethical in war. The book closely examines particular practices of warfare, such as targeting, the use of cultural knowledge, and ethics training for soldiers. What emerges is that instead of constraining violence, the commitment to ethics enables and enhances it. The book argues that the production of ethical war relies on an impossible but obscured separation between ethics and politics, that is, the problematic politics of ethics, and reflects on the need to make decisions at the limit of ethics.
Contents:
1: Introduction
2: The Paradox of Ethical War and the Politics of Ethics
3: Targeting: Precision Bombing and the Production of Ethics
4: Culture: Knowledge of the People as Technology of Ethics
5: Ethics Education: Ethics as Ethos and the Impossibly Good Soldier
6: The Politics of War at the Limits of Ethics
 Laura Auslander and Tara Zahra (eds), Objects of War: the material culture of conflict and displacement (Cornell, May 2018)
Laura Auslander and Tara Zahra (eds), Objects of War: the material culture of conflict and displacement (Cornell, May 2018)
Historians have become increasingly interested in material culture as both a category of analysis and as a teaching tool. And yet the profession tends to be suspicious of things; words are its stock-in-trade. What new insights can historians gain about the past by thinking about things? A central object (and consequence) of modern warfare is the radical destruction and transformation of the material world. And yet we know little about the role of material culture in the history of war and forced displacement: objects carried in flight; objects stolen on battlefields; objects expropriated, reappropriated, and remembered.
Objects of War illuminates the ways in which people have used things to grapple with the social, cultural, and psychological upheavals wrought by war and forced displacement. Chapters consider theft and pillaging as strategies of conquest; soldiers’ relationships with their weapons; and the use of clothing and domestic goods by prisoners of war, extermination camp inmates, freed people and refugees to make claims and to create a kind of normalcy.
While studies of migration and material culture have proliferated in recent years, as have histories of the Napoleonic, colonial, World Wars, and postcolonial wars, few have focused on the movement of people and things in times of war across two centuries. This focus, in combination with a broad temporal canvas, serves historians and others well as they seek to push beyond the written word.
 Eli Berman, Joseph H. Felter and Jacob N. Shapiro, Small Wars, Big Data: The Information Revolution in Modern Conflict (Princeton, June 2018):
Eli Berman, Joseph H. Felter and Jacob N. Shapiro, Small Wars, Big Data: The Information Revolution in Modern Conflict (Princeton, June 2018):
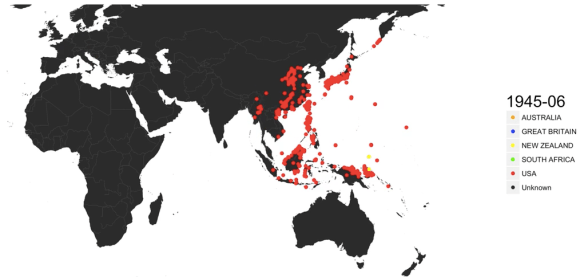
The way wars are fought has changed starkly over the past sixty years. International military campaigns used to play out between large armies at central fronts. Today’s conflicts find major powers facing rebel insurgencies that deploy elusive methods, from improvised explosives to terrorist attacks. Small Wars, Big Data presents a transformative understanding of these contemporary confrontations and how they should be fought. The authors show that a revolution in the study of conflict–enabled by vast data, rich qualitative evidence, and modern methods―yields new insights into terrorism, civil wars, and foreign interventions. Modern warfare is not about struggles over territory but over people; civilians―and the information they might choose to provide―can turn the tide at critical junctures.
The authors draw practical lessons from the past two decades of conflict in locations ranging from Latin America and the Middle East to Central and Southeast Asia. Building an information-centric understanding of insurgencies, the authors examine the relationships between rebels, the government, and civilians. This approach serves as a springboard for exploring other aspects of modern conflict, including the suppression of rebel activity, the role of mobile communications networks, the links between aid and violence, and why conventional military methods might provide short-term success but undermine lasting peace. Ultimately the authors show how the stronger side can almost always win the villages, but why that does not guarantee winning the war.
Small Wars, Big Data provides groundbreaking perspectives for how small wars can be better strategized and favorably won to the benefit of the local population.
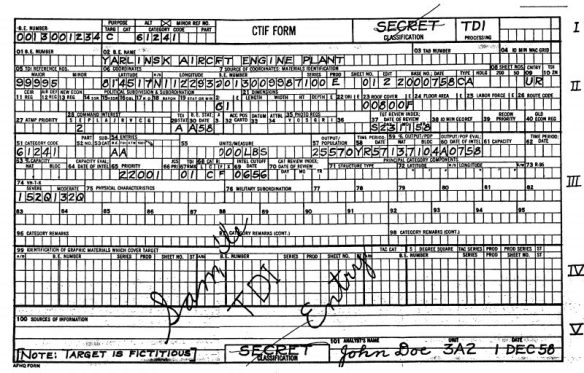 Ever since I first wrote about the US Air Force’s Bombing Encyclopedia of the World (see here, here, and here) I’ve received endless e-mails about the project, but now there is a wonderful article by Elliott Child – ‘Through the wringer: Mass interrogation and United States air force targeting intelligence in the early cold war’ – that goes into extraordinary detail about the back-story. It’s just appeared on the Political Geography website (https://doi.org/10.1016/j.polgeo.2019.102052).
Ever since I first wrote about the US Air Force’s Bombing Encyclopedia of the World (see here, here, and here) I’ve received endless e-mails about the project, but now there is a wonderful article by Elliott Child – ‘Through the wringer: Mass interrogation and United States air force targeting intelligence in the early cold war’ – that goes into extraordinary detail about the back-story. It’s just appeared on the Political Geography website (https://doi.org/10.1016/j.polgeo.2019.102052).