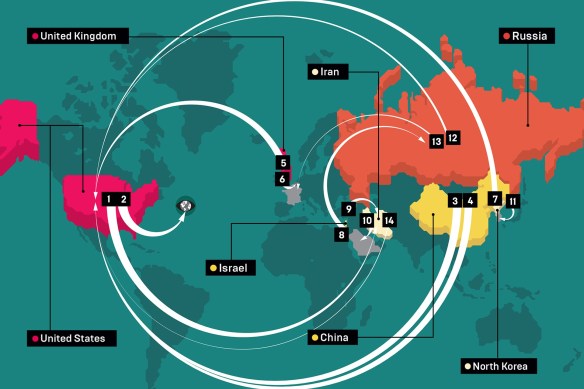
The latest issue of Wired has a simply schematic map of ‘an invisible but vast war zone’ created by cyberattacks:
Every month, it seems, a mammoth cyberattack sponsored by a nation state comes to light. In recent years, more than 20 countries have announced their intent to launch or beef up their offensive cyber capabilities. The result is a burgeoning digital arms race that presents a major threat to the security of our data.
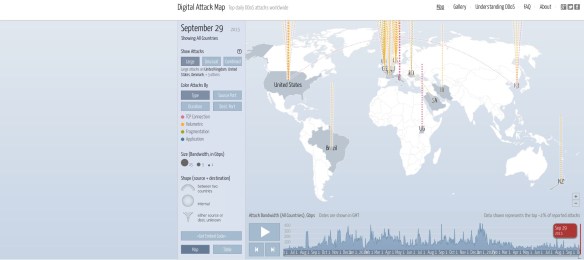
But they are very late to the game (and there are also many internal threats to ‘the security of our data’: think NSA or GCHQ). In October 2013 Google Ideas in collaboration with Arbor Networks launched an interactive map of daily Distributed Denial of Service (DDoS) attacks that attempt to make an online service unavailable by overwhelming it with traffic from multiple sources :
According to Arbor Networks,
Attackers build networks of infected computers, known as ‘botnets’, by spreading malicious software through emails, websites and social media. Once infected, these machines can be controlled remotely, without their owners’ knowledge, and used like an army to launch an attack against any target. Some botnets are millions of machines strong. Botnets can generate huge floods of traffic to overwhelm a target. These floods can be generated in multiple ways, such as sending more connection requests than a server can handle, or having computers send the victim huge amounts of random data to use up the target’s bandwidth. Some attacks are so big they can max out a country’s international cable capacity. Specialized online marketplaces exist to buy and sell botnets or individual DDoS attacks. Using these underground markets, anyone can pay a nominal fee to silence websites they disagree with or disrupt an organization’s online operations. A week-long DDoS attack, capable of taking a small organization offline can cost as little as $150.
I discussed these, and connected them to militarised cyberattacks in ‘The everywhere war’ [DOWNLOADS tab].
The site provides an illuminating typology of attacks – TCP connection attacks that attempt to use up all available connections; Volumetric attacks that use up bandwidth; Fragmentation attacks that send a flood of TCP or UDP fragments to a victim, overwhelming their ability to re-assemble the streams and severely reducing performance; and Application attacks that target applications.
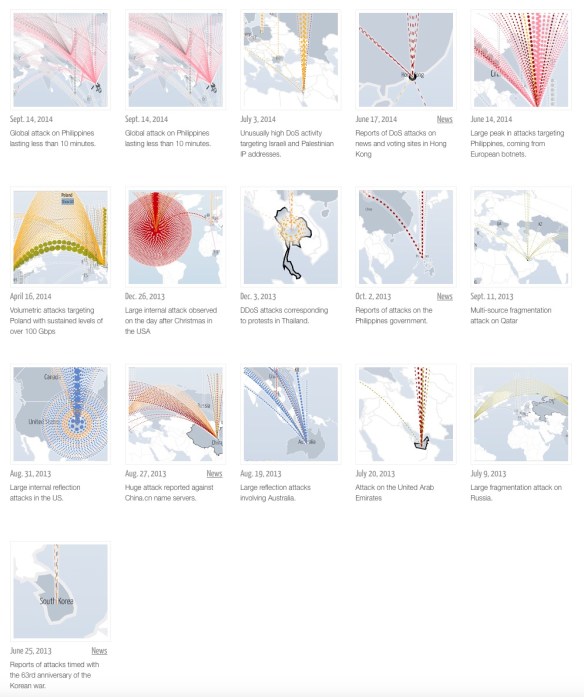
There is also an instructive gallery of major attacks:
And in 2014 another internet security company, Norse, released a live stream of origins and targets of attack; I’ve pasted a screenshot below but there is also a YouTube video here.
The image above — which looks like Missile Command on steroids — shows just a snippet of hacking attempts around the world, the countries from which they originate, and the countries that they are attacking.
In reality, the attackers are hitting what Norse calls honey pots — special traps designed to detect unwanted network intrusions by hackers. It’s important to note that the location an attack comes from isn’t necessarily its true origin, as hackers can make an attack look like it’s coming from one place when it’s really coming from another.
You can find a list of other cyber attack maps at CTF365 here.