I’ve emphasised the networks in which drone operations take place several times on this blog, and I’ll have more to say about it (and, crucially, the satellite links involved) very shortly. But this applies to all domains in which advanced militaries now operate. In 2012 Army magazine (62: 6) put it like this:
The world in which U.S. forces operate is increasingly wireless and computer network-based. Rapidly evolving information technologies are expanding the speed, capacity, agility, efficiency and usefulness of modern networks. The prolif- eration of these systems is changing the way humans interact with each other and their environment, including military operations. This creates conditions that will make U.S. forces increasingly dependent on these technologies and require soldiers to counter technology-empowered and so- phisticated adversaries who can utilize commercial indus- try and the network as their primary combat developers. This broad and rapidly changing [Operational Environment] will present a plethora of potential threats and opportunities that are primarily limited by our own—and our opponents’—imagination, causing the Army to operate within a cyberspace domain and EMS [Electromagnetic Spectrum] that are increasingly congested and contested.
The authors went on to emphasise the convergence of ‘cyber and EMS capabilities’ (and, not coincidentally to my interest in satellite communications, the intersections between commercial and military systems):
Commercial and military systems are increasingly reliant on both as networks and telecommunication infrastructures expand their use of wireless means. This is particularly important for collaborative systems that require connectivity to operate effectively. The synergistic effect of these networks is a significant reason why EW [electronic warfare], EMSO [EMS operations] and cyber operations must be viewed as interrelated and interdependent.
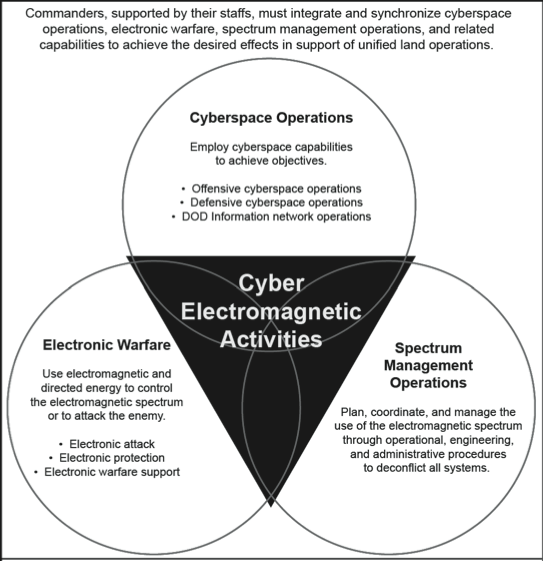
The Pentagon has now published its first Field Manual on Cyber Electromagnetic Activities (FM 3-38). If you are still wondering what these are, and why I’ve described them as the ‘other side’ of NSA (and by extension, GCHQ and the other ‘Five Eyes’) global surveillance operations, this is what the manual says:
Cyber electromagnetic activities are activities leveraged to seize, retain, and exploit an advantage over adversaries and enemies in both cyberspace and the electromagnetic spectrum, while simultaneously denying and degrading adversary and enemy use of the same and protecting the mission command system (ADRP 3-0). CEMA consist of cyberspace operations (CO), electronic warfare (EW), and spectrum management operations (SMO).
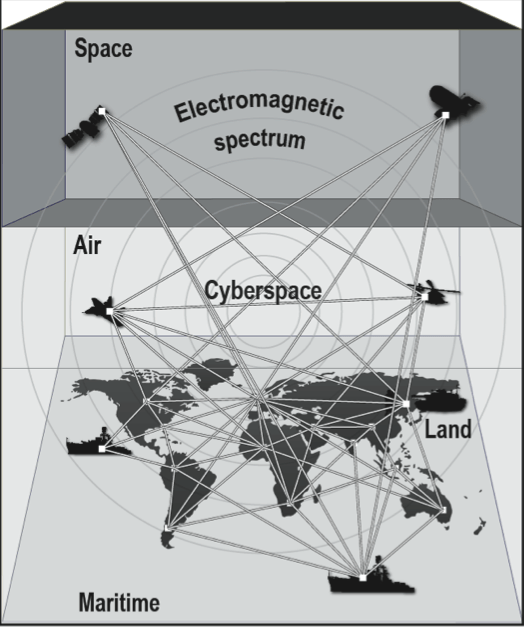
The FM – and remember this is doctrine: we have a long way to go before we are able to probe into practice – diagrams the relation between the ‘five domains’ of US military operations (air, land, sea, space and cyberspace) and the electromagnetic spectrum like this:
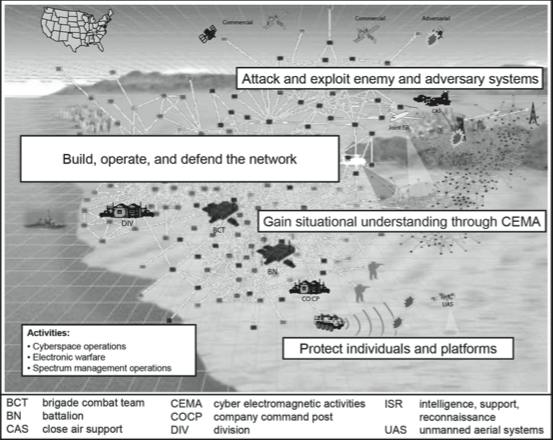
Operationally, for ‘unified land operations’ (this is a US Army manual, remember) this translates into undertaking Cyber Electromagnetic Activities (CEMA) thus:
You can find a short discussion of the pre-history behind the Field Manual here.
I’m going to work my way through the manual in detail, and think through its implications for what I already know about cyberwar (even if Thomas Rid thinks it will never take place). I sketched out some of my early ideas in ‘The everywhere war’ (DOWNLOADS tab), largely in relation to Stuxnet and cyber-attacks on Iran’s nuclear programme, but there have been many more developments and revelations since then, so watch this space.